Network breaches happen daily in the digital age, so it is imperative that we stand vigilant in our fight against persistent malware threats, while supporting standards that safeguard data privacy and enhances the effective communication of cyberthreat incidents and identified intrusion indicators.
Rapid response time is a priority. Dwell time must be kept to a minimum.
The revelation [Oct 2014] that a Russian crime ring amassed the world’s largest known collection of stolen Internet credentials, including 1.2 billion username and password combinations and over 500 million email addresses, simply reinforces the fact that cybercrime is something that affects both private and public sector organizations of every size. Spyware and malware are among an organization’s biggest threats and often go unnoticed until it’s too late, due to their elusive nature.
Malware is commonly implemented with a simple one-line script, injected into a compromised website and made to look like normal code. Challenging breeds of malware continue to evolve and become more dangerous while reaching new levels of complexity.

The Train Has Left the Station
It is an unfortunate fact that both private and public sector networks are under constant attack and every organization connected to the internet is a constant target for network intrusion, therefore dwell time and response time is a critical IT/IS priority.
Stealthly criminals infiltrate networks without consent, in several hostile and intrusive ways, including the installation of rootkits, that provide masked administrator-level intrusion to gain root or privileged access and control of the OS. One leading antiroot kit utility is available from Kaspersky labs in Russia, [it will detect and removes known rootkits TDSS, SST, Pihar, ZeroAccess, Sinowal, Whistler, Phanta, Trup, Stoned, RLoader, Cmoser, Cidox), Russian Federation laws apply.
When a network breach is first discovered, every moment is critical. Not only should the organization shut down the network attack, but it must work to minimize resulting collateral damage — and it must do so quickly. Once an intruder has gained super user access, they now control the system.

Malware is defined by its hidden malicious intent.
It’s a race in real time. It’s a race in calendar time. Sometimes, a network may not detect malware until after an infection occurs and vulnerabilities are exploited.
Professionals maintain internal controls, with security updating systems to ensure compliance with industry standards, thus avoiding administrative, criminal or civil liability against the organization and it’s directors.
The Honourable Vic Toews, P.C., Q.C., M.P. Minister of Public Safety
“These criminal groups are breaking into our computer systems, searching through our files, and causing our systems to crash. They are stealing our industrial and national security secrets, and our personal identities”.

Attacks to government and client networks are not only becoming more complex, but also more sophisticated. A GAO study finds that reported attacks increased 782% between 2006 and 2012.
Attacks have been increasing in both volume and speed by cyber criminals attempting to gain access to government networks.
“Recent media attention has highlighted the proliferation of security breachesaffecting us all. These security failures have not only resulted in significant expense to the organizations affected, but have significantly damaged trust and reputation. The sensitive data embedded within your networks and systems is a high-value target to hackers“.
Patrick Malcolm, Digital Forensics and Cybersecurity Expert Trainer, National Capital Region [Ottawa, Canada]
M-Trends Threat report: A View from the Front Lines
Cybersecurity has gone from a niche IT issue to a boardroom priority and Cross-Agency-Priority (CAP) for business and government organizations.
Executive Order — Promoting Private Sector Cybersecurity Information Sharing
U.S. President Obama signed an executive order that aims to better share cybersecurity threat information.
Below is a ‘Report Template’ for Threat Intelligence and Incident Response
When handling intrusions, incident responders often struggle with obtaining and organizing the intelligence related to the actions taken by the intruder and the targeted organizations. Examining all aspects of the event and communicating with internal and external constituents is a challenge in such strenuous circumstances.
The following template is a Threat Intelligence and Incident Response Report which aims to ease this burden. This report provides a framework for capturing the key details and documenting them in a comprehensive, well-structured manner. Zeltser Security Corp – https://zeltser.com/cyber-threat-intel-and-ir-report-template/
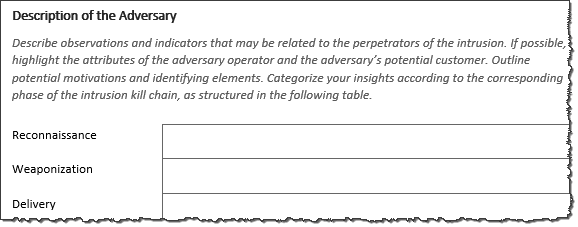
This template leverages several models in the cyberthreat intelligence (CTI) domain, such as the Intrusion Kill Chain, Campaign Correlation, the Courses of Action Matrix and the Diamond Model. The use of these frameworks helps guide threat intelligence gathering efforts and inform incident response actions.
Download the Report Template
You can download the editable report template in the Microsoft Word format. You can also view it in the PDF format or in the mind map XMind format.
The template is distributed according to the Creative Commons Attribution license (CC BY 4.0), which basically allows you to use it in any way you wish, including commercial purposes, as long as you credit Lenny Zeltser for the creation of the template.
Conclusion
As cyber criminals become more sophisticated and adept in exploiting information technology, it becomes even more important for both private and public sector organizations to develop a risk mitigation strategy to detect, attribute and filter out persistent, malicious threats and adversary operators from our online communities.




Leave a Reply
You must be logged in to post a comment.