This blog post is an excerpt from GovLoop’s recent research brief, Protecting Your Most High-Value Assets with the NIST Cybersecurity Framework. Download the full report here.
The Trump administration is doubling down on protecting our nation’s most critical assets by enhancing the government’s cyber posture. In May 2017, the President issued an executive order titled “Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure.” Additionally, the fiscal 2019 budget highlights integrating cybersecurity into every aspect of IT modernization and making it a priority at all federal agencies.
To meet these mandates and obligations, agencies are turning to the National Institute of Standards and Technology’s Cybersecurity Framework. NIST developed the CSF in collaboration with industry and government to set standards, guidelines and best practices to promote the protection of critical infrastructure and improve government security. It is now a mandate that agencies must meet under the current administration.
The CSF Core is a “set of cybersecurity activities, desired outcomes and applicable references common across critical infrastructure sectors.” The core consists of five concurrent and continuous functions: Identify, Protect, Detect, Respond and Recover.
We’ve previously talked about adopting the CSF and identifying your most valuable assets and data. Now it’s time to discuss the next phase, Protect, which ensures that data at rest and in transit is secure.
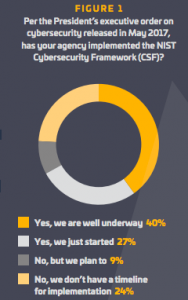
To learn more about the CSF’s usage, perception and outcomes in government, particularly its Protect function, GovLoop teamed with cybersecurity firms Symantec and DLT to survey 79 federal employees. Only 40 percent of respondents said they have implemented the CSF, and another 27 percent are just getting started since the release of the President’s cybersecurity executive order (See Figure 1).
The most recent Federal Information Modernization Security Act report, issued to Congress in 2016, shows 30,899 reported cyber incidents that led to the compromise of information or system functionality that year. What’s more, attacks using ransomware are getting costlier for the government. While the average ransomware demand actually decreased in 2017 to $522, the number of ransomware variants increased by 46 percent. Additionally, 5.4 billion WannaCry attacks were blocked.
For 2018 and beyond, the pressure is on federal agencies to make sure they are doing their utmost to protect critical assets. Within 30 days of the Final IT Modernization Report, NIST was tasked with providing the Office of Management and Budget with “a plan to promote a risk management culture that focuses agency effort on the operational performance and compliance of their most valuable systems.”
The goal of the CSF’s Protect function is to “develop and implement appropriate safeguards to ensure delivery of critical infrastructure services. The Protect function supports the ability to limit or contain the impact of a potential cybersecurity event.” Methods include identity management and access control, awareness and training, data security, maintenance and protective technology.
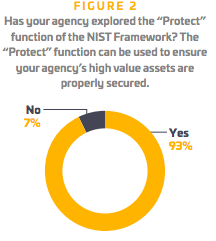
For example, implementing two-factor authentication for employee devices is a simple and significant first step to meeting the protection requirements. Fortunately, agencies are already prioritizing it. According to our survey, about 93 percent of federal respondents have at least explored the Protect function (See Figure 2).
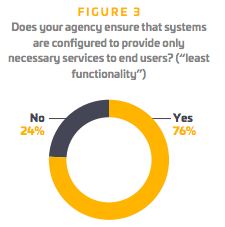
Additionally, about 76 percent of respondents said they believe their agencies ensure that systems are configured to provide only necessary services to end users in a “least functionality” manner (See Figure 3).
But to meet the Trump administration’s recent mandates and stay ahead of malicious attackers, it’s critical to take “exploring the Protect function” to the next level. “Cybersecurity threats continue to exploit the increased complexity and connectivity of critical infrastructure systems, placing the nation’s security, economy and public safety and health at risk,” the CSF states.
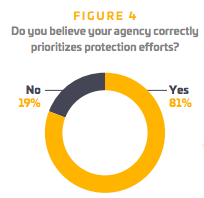
Agencies must step up their efforts not only in implementing the overall CSF, but also in following through with the Protect function. Federal officials seem to understand the importance of prioritizing the protection of critical assets and data. Our survey shows that about 81 percent of respondents believe they correctly prioritize their agency’s protection efforts (See Figure 4).
Regardless of where your agency stands in prioritizing the CSF’s Protect function, the impetus is clear: Cybersecurity attacks are increasing in number and complexity, and agencies stand to lose too much money and public trust to fail at defending the nation’s critical infrastructure.





Cyber is a major issue for governments at all levels. Watching how the NIST Cyber Framework is implemented will definitely be interesting. Thanks for sharing.