By the time Jan. 15 rolls around, 90 days will have passed since the Homeland Security Department issued Binding Operational Directive 18-01 (BOD 18-01), designed to curb email and web security hazards.
This marks the point by which all federal agencies must begin to show email security enhancements — in other words, to begin implementing the Domain-based Message Authentication, Reporting and Conformance (DMARC) process. The protocol “is a way to make it easier for email senders and receivers to determine whether or not a given message is legitimately from the sender, and what to do if it isn’t,” according to dmarc.org. “This makes it easier to identify spam and phishing messages, and keep them out of peoples’ inboxes.”
So how effectively are agencies making changes?
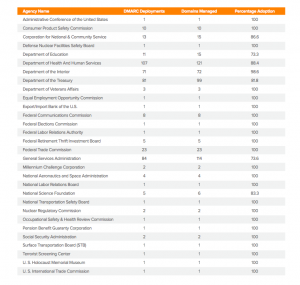
According to a progress report published in December by email security company Agari, the DMARC adoption rate has increased month over month. But as of Dec. 19, still fewer than half of the 1,106 federal government domains had in fact met the basic DMARC requirements. Below is a snapshot of some agencies.
“Several agencies have already implemented DMARC, while many others continue to make great progress as they work to adopt it,” according to a DHS official. The official added that a majority of federal civilian agencies were on schedule to meet all email and web-related deadlines set by the directive.
Email security threats are a pressing concern for government. Between the end of June 2017 and end of December 2017, government domains on the Agari Email Trust Network received nearly 69 million malicious emails — about 8 percent of all received emails.
DMARC Adoption Policies
It’s helpful to understand the different levels of DMARC policy adoption, as the DHS timeline is largely built around them. For more information, visit dmarc.org.
1. None (monitor) policy. The “p=none” policy is the minimal level required of federal agencies to implement by Jan. 15. Domain owners must monitor for authentication abuse, but they don’t have to take any action to prevent it. This is effectively the first step in the process to better security.
2. Quarantine policy. At the time Agari published its December report, less than 1 percent (five domains) were at this initial level of enforcement. With this policy, all messages that fail DMARC tests are sent into the spam folder.
3. Reject policy. The “p=reject” policy blocks all messages that fail authentication. Per DHS mandates, all government agency domains need to adopt this policy by Oct. 16, 2018.
Key stats
- 47 percent of domains (523 of 1,106) had adopted “p=none” policy as of Dec. 19, 2017. All are required to adopt by Jan. 15, 2018.
- 15 percent of domains (164 of 1,106) had adopted “p=reject” policy as of Dec. 19, 2017. All are required to adopt by Oct. 16, 2018.
- 85.84 percent of domains (406 of 473) protected by Agari’s services were targeted with malicious emails during a six-month period ending Dec. 26, 2017.




Leave a Reply
You must be logged in to post a comment.