“The idea of Zero Trust is not new,” said Fortinet’s Field Chief Information Security Officer, Jim Richberg. “It goes back 30 years. But the evolution of IT and of the threat actors are making it more important now.” In fact, much of the foundational work defining the requirements and principles of Zero Trust computing was done by the federal government.
Mainframe computing with dedicated computer rooms and limited network connections made it possible in the past century to protect the IT infrastructure with physical security. The client/server model expanded the perimeter, making it virtual rather than physical. Firewalls and antivirus products defended this new perimeter. They are outward-facing tools that assumed the bad guys were outside trying to get in.
Despite the expenditure of millions of dollars on these tools, the Government Accountability Office (GAO) has designated national cybersecurity as a high-risk area continuously since 1997, declaring in its most recent report that “federal agencies…need to take urgent actions to implement a comprehensive cybersecurity strategy, perform effective oversight, secure federal systems, and protect cyber critical infrastructure, privacy, and sensitive data.”
Today, with the rapid adoption of cloud computing, remote access by mobile devices and the Internet of Things, the network perimeter has effectively disappeared, making outward-facing defenses as outdated as the Maginot Line.
More than 70% of respondents said their agencies had a very clear or somewhat clear picture of the people and devices on their networks. But the steady drumbeat of data breach reports from government and private industry shows that this picture is not effectively protecting their data and other IT resources.
Ponemon’s latest “Cost of Data Breach Report” analyzes data breach costs reported by 507 organizations across 16 regions and 17 industries. The average total cost of a data breach to an organization is $3.92 million globally. The U.S. average is the highest in the world at $8.19 million. The “2020 Annual Cybercrime Report” by Cybersecurity Ventures estimates that “cybercrime will cost the world $6 trillion annually by 2021, up from $3 trillion in 2015.”
Financial loss is not the only measure of the threat. Sensitive and classified government data is also at risk in agencies, from insiders and outsiders alike:
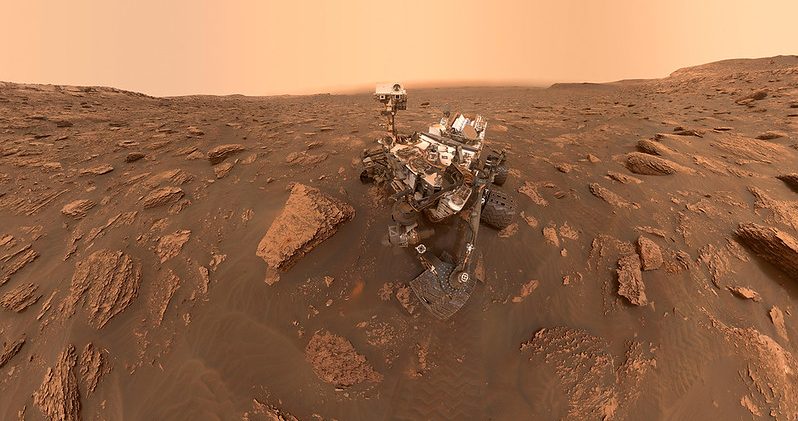
- According to a NASA Office of the Inspector General (IG) report from June 2019, an unauthorized person accessed NASA’s Jet Propulsion Laboratory, making off with highly sensitive information, including details about NASA’s Curiosity Rover. The hacker went undetected for 10 months and had access to many critical projects.
- Reuters reported on Feb. 20, 2020, that the Defense Information Systems Agency (DISA), which provides security for sensitive executive branch communications, believes a breach between May and July 2019 could have compromised data on its systems.
- The Washington Post on March 22, 2020, reported a “major privacy incident” at the Federal Emergency Management Agency (FEMA): a possible breach of information on 2.5 million persons who had sought disaster assistance. An IG report states that FEMA became aware of the problem in December 2019, when the agency installed a data filter to spot inappropriate sharing of the information.
There is an opportunity to improve current cybersecurity models to better meet the needs of today’s networks. A Zero Trust platform uses visibility into IT networks and systems to identify all users and devices and assign only appropriate access privileges. It also monitors activities to identify, stop and remediate malicious or inappropriate activity. All those components will improve today’s security models.
This article is an excerpt from GovLoop’s recent report, “Zero Trust: An Updated Approach to Agency Cybersecurity.” Download the full report here.




Leave a Reply
You must be logged in to post a comment.