Transformation
This part is the fourth and final in this series. This article rounds up the activities undertaken in the first three quarters of the Chief Information Security Officer 365 days journey and focuses on future planning based on the collective experience. I discussed the importance of “continuous improvement” in the third article, which is key ingredient for any successful program. It is also about the transformation of the organization based on the results of the foundational activities and visible results to move the cybersecurity maturity needle in right direction.
Looking Forward!
After building the program for three quarters, seeking feedback from the stakeholders and making course corrections, a CISO should look forward. During this journey, any CISO will be pleasantly surprised by the information shared by the stakeholders, customers and vendors. A key recommendation will be to create a support group which can provide what a leader needs to do to be successful and not what he/she wants to hear. I have also discussed this concept in my previous article on “cybersecurity ecosystem.”
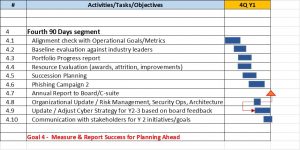
Fourth Quarter Goals – Measure and Report Success for Planning Ahead
As the first 365 days come to an end for a CISO’s tenure, looking back will provide a view of the path with milestones achieved, lessons learned and relationships formed.
Alignment Check With Operational Goals/Metrics
This is the socialization step for metrics and dashboard integration with the cyber strategy. Please note that these can be revised along with the cyber strategy, as these will evolve and change based on other factors.
Baseline Evaluation Against Industry leaders
While embarking on a foundational program, it is important to benchmark the progress with leaders within the same industry segment/vertical for adopting best practices. This enables healthy competition and the infusion of new initiatives to stay at the top.
Portfolio Progress Report
An annual progress report, which can be provide an in-depth status of the cyber strategy execution, is critical. This is an opportunity to bring transparency and stay on course.
Resource Evaluation for Future Planning (Awards, Attrition and Evaluation)
Based on the adjustments to the portfolio and strategy, resource projections can be completed for future periods, driving funding requests. With cyber professionals in high demand, it provides leadership the chance to proactively plan the resources for projects with sufficient lead time. Please note that it also proactively assists in planning for natural attrition.
Succession Planning
Leaders evolve and move, and hence succession planning is critical for organizational success. Due to a high level of attrition in cybersecurity world at all levels, I recommend that succession planning should be done for the leadership team first to minimize the organizational impact and reduce the risk.
Phishing Campaign 2
Per an earlier statement, it’s a good practice to have two phishing campaigns a year to review the trend of employee security awareness . It also assists with evaluation of current security awareness programs and making changes.
Annual Report to the Board/C-Suite
Sharing the annual report to the board and C-suite will only enhance the credibility and confidence in the program and leadership. The annual report should focus on state of cybersecurity for the organization, strategy, risks and impact on the business operations, and future plans. Additionally, reference material should also be provided in support for the key components of the annual report.
Organizational Update (Risk Management, Security Ops, Architecture)
While focusing on the strategic fourth quarter activities, it is tactically important to check the progress of the three critical domains of the cybersecurity organizations – risk management, security operations and architecture – based on their annual goals. Goal adjustments/updates based on the annual experience will only improve the motivation and performance of the organization.
Update/Adjust Cyber Strategy for Y2- 3 Based on the Feedback
My team and leadership have often asked: “What after 365 days?” This activity accounts for current accomplishments, remaining work per the strategy, organizational appetite for funding and provides an updated roadmap for Year 2 and 3. This is an extremely important activity and deliverable to set the tone for post-365 days.
Communication With Stakeholders for the Year 2 Initiatives/Goals
As I mentioned earlier in the article, LOOKING FORWARD is an important aspect of this phase – planning and setting organizational strategy and direction charts the course for the next 365 days, leveraging the foundation built in the first 365 days completes the circle.
Key Takeaways
- Assessment, Strategic Planning & Operations are key to a successful cybersecurity program. Knowing what you don’t know is crucial to strategic planning and operations.
- Collaboration and innovation are crucial to survive and future proof. Become part of the local and national CISO forums such as SIM, Gartner, CSO50 and others to collaborate with fellow CISOs. These are excellent learning opportunities and share innovation.
- Keep business operations and the board always in mind. Business operations are the backbone of the organization and cyber should provide the security to operate with business continuity in mind.
- Train, exercise and exercise again! The best laid plans are no good if not tested regularly. The plans provide an opportunity to test use cases, scenarios for constructive feedback and organizational preparedness. Please note that with current COVID-19 pandemic, this activity has become very critical.
Rajiv has more than 25 years of information technology strategy, operations, large systems integration, cyber security and program management experience. Rajiv is a principal with Plante Moran management Consulting, cybersecurity practice after serving as Chief Information Security Officer (CISO) for the Department of Technology, Management and Budget, State of Michigan.





Great insight into an important role. Thank you for sharing!