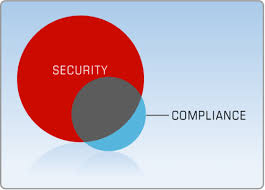
Underlying any strategic or tactical projects that federal Chief Human Capital Officers (CHCOs) consider undertaking, are the issues of security and privacy. While the choice of an optimal, efficient and feature-rich talent management solution is critical and necessary to help an agency achieve its goals and realize its mission, without stringent security considerations, even the most feature-rich and user-friendly solution is unacceptable and a nonstarter.
This is the third post in a series looking at various strategic human capital management issues facing federal CHCOs. While the primary focus of the series is on the key pillars of talent management, such as talent acquisition, performance management, workforce planning and more, the security of CHCOs’ HR systems and entire agency must always be at the forefront of their efforts. Given this importance, I wanted to focus on this issue as it relates to strategic federal human capital management.
Even as federal human capital leaders look to implement strategic plans while embracing shorter-term, tactical initiatives, they can never take their eye off critical security issues.
Options to Ensure Security Compliance
Federal agencies Chief Information Officers (CIOs) require and deserve a high level of confidence for any third-party talent management system deployed in their agency. The top three factors impacting this comfort level include:
- Involvement of a trusted organization to certify security of the proposed solution.
- A trusted party to provide ongoing security oversight and compliance monitoring of the solution.
- Strict access control to sensitive agency and applicant information by agency staff and contractors.
The ultimate concern is to have assurance that there are adequate information security safeguards in place. Any HR solution selected needs to ensure this protection.
The solution must provide the agency CIO with the assurances needed to implement the solution, while also providing adequate cost efficiencies. If a solution meets the security needs but drains resources to the point that it is unmanageable, it is also likely not a viable solution. Ideally, it would save money too.
Federal Government Security Frameworks

There are two primary frameworks addressing security assessment for federal agencies that ultimately need to be considered:
- FedRAMP is the U.S. government’s risk management program for Cloud Computing procurements. It is an authorization process that requires Cloud Service Providers to conduct an independent security assessment and a sponsoring Government Agency to issue an Authority to Operate (ATO) letter and perform ongoing FedRAMP Continuous Monitoring activities. FedRAMP accredited third-party assessment organizations (3PAO) are elite representatives of the Information Security industry. The cost of FedRAMP assessment is typically borne by the Service Provider and shared between Cloud tenants.
- FISMA (Federal Information Security Management Act) can be considered as a predecessor of FedRAMP for mostly non-cloud systems, but can in certain cases apply to dedicated systems deployed on top of a Cloud. FISMA evolved from the Federal Information Security Management Act of 2002 that mandates a process to strengthen the security posture of government information systems, and compliance is required by law for federal agencies. FISMA-compliant generally refers to meeting the controls identified in NIST security guidance.
Cloud vs. Dedicated Hosting
The hosting options available to federal agencies can also be broken into two high-level categories:
- Cloud. With cloud-based hosting, typically the cloud provider ensures the security and privacy of the system. Software vendors may have partnered with a FedRAMP-authorized cloud service (e.g. Amazon Web Services) to provide a robust and secure hosting platform, where the vendor takes care of resource procurement and management on behalf of customers. With cloud hosting, either FedRAMP or FISMA solutions can be implemented:
– FedRAMP can be used for multi-tenant SaaS Natural Talent Federal delivery (sponsored by the FedRAMP Joint Authorization Board or another Government Agency).
– The FISMA authorization path may be taken in some cases for single-tenant virtual environments.
- Dedicated data center. Some agencies may choose to use dedicated hardware and software for hosting of their talent management system, which could then be managed by a Government Datacenter staff. The FISMA authorization path would be taken with this approach. However, this is typically the most costly option in the long run.
Legacy Systems and Cost of Maintaining In-House Systems
With security threats facing virtually every federal institution, the vulnerability of federal agencies is top of mind of our federal government leaders. The threats are exacerbated due to the fact that many government agencies use older, legacy systems that were not designed to resist today’s threats. These systems not only increase vulnerability to computer attacks, they also increase expenses because of their high cost to maintain, and they impair agencies’ ability to adapt to an ever-changing environment and continual threats.

As Federal Computer Week pointed out recently, “the recent hacks of legacy systems at the Office of Personnel Management are a reminder that government needs to move off of antiquated IT and into modern systems built with integrated security.” Tony Scott, the federal Chief Information Officer, recently stated that “we’re at a critical inflection point at the IT industry as a whole. Not just because of cybersecurity, but it’s sort of a big drive for it, we have to make investment and we have to really start moving off some of these older constructs and doing it with some sense of urgency.”
And while security is of critical importance, the cost and ongoing maintenance of systems can’t be forgotten, as they present their own set of problems. In the current environment, modern systems should bring the additional benefit of saving money. Federal News Radio recently stated “the challenge of archaic systems is not new for the government. The annual federal CIO Survey by Grant Thornton and the Professional Services Council found respondents say they still spend about 75 percent of their budget maintaining older systems and only 25 percent for development.” Undoubtedly, this is an area that CIOs cannot afford to overlook. Therefore, a solution that meets security needs but that also entails less ongoing work for managing budgets, managing people and ongoing security and compliance monitoring as well is preferred over a high-cost, high-maintenance solution.
Security — the Foundation for Strategic Human Capital Management
While federal Chief Human Capital Officers and their teams consider HR technology options to help them fulfill their agencies’ missions, they can never lose sight of ensuring the most stringent security capabilities. Even as possible short-term changes and deployments are implemented, the underlying security of their HR systems cannot be overlooked with regard to any technology selected. Ensuring the highest level of security with no compromise to HR functionality will enable HR leaders to reach their strategic goals as they evolve towards a complete integrated talent management strategy.





Leave a Reply
You must be logged in to post a comment.