This blog post is an excerpt from GovLoop’s recent guide “State and Local Government: 8 Tech Challenges and Solutions.” In it, we provide an overview of case studies from governments across the country. Download the full guide here.
An interview with Paul Groll, Deputy Chief Security Officer of Michigan and Executive Sponsor of the Michigan Cyber Civilian Corps
Challenge: Preparing for a Cyberattack
It’s become something of a recurring nightmare. A malicious computing force nds a crack in your system’s defenses, squeezes through it, then moves around as it pleases. Sometimes it shuts down integral services, sometimes it takes off with sensitive user information.
These realities weigh heavily on the minds of IT professionals across the country, and maybe none more so than those within government. And although no amount of resources can guarantee absolute immunity from an attack, more money would always be nice.
But that’s not realistic for many agencies, so some have tried to combat the issue with more creative solutions. Michigan is among this group. Since 2013, when Gov. Rick Snyder proposed the idea at the North American International Cyber Summit, the state has worked to assemble the nation’s first team of volunteer cybersecurity experts: the Michigan Cyber Civilian Corps (MiC3).
“As the landscape became more and more peppered with cyberattacks left and right, the question is, if we really get a devastating attack on critical infrastructure, does the state have the resources to respond on our own?” said Paul Groll, Michigan’s Deputy Chief Security Officer and MiC3’s Executive Sponsor. “Or is something else needed above and beyond?”
Because there was little in the way of a roadmap for creating this kind of emergency response unit, MiC3 had to begin setting its own foundation and working out kinks along the way.
Solution
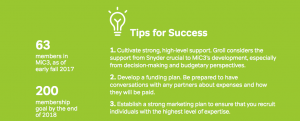
As of late September 2017, MiC3 consisted of 63 volunteers, with more in the pipeline. It’s a fast-growing group of cybersecurity experts, spurred by Snyder’s ambitious objective to grow MiC3 to 200 volunteers by the end of 2018.
Each member must satisfy a set of requirements before being welcomed to the corps. First, all applicants must have at least one major certification in a core security competency. In addition to that, MiC3 prefers its members to have at least two years of hands-on cybersecurity experience.
If they meet these requirements, applicants must take a series of online tests to prove comprehension of networking and security concepts. If they pass four of the five tests, they’re offered membership, which comes with a .gov email address and an impressive amount of training resources. If they pass only two or three tests, MiC3 tries to set them up with a plan to further hone their skills.
“We’re eager to foster the development of cyber skills in Michigan, and we will assist them in getting a curriculum put together so that they can study what they’re missing and try again,” Groll said.
The team hasn’t had to respond to a crisis yet, but Groll explained how that would happen. In the case of an attack, the state would first blast an email out to MiC3’s members, then post on the group Slack channel. If the response required specific expertise or geographic locations, Groll said his co-workers would begin calling individual members.
“The concept of this Cyber Civilian Corps was floated with the idea that they would function pretty much after the model of a volunteer fire department,” Groll said.
That sort of speed in crisis management lends itself to another analogy — that of an emergency room. MiC3’s purpose is to stabilize the IT system under attack and keep it upright. After the immediate threat has been withstood, the corps can then pass things off to a more conventional commercial service team, Groll said.
This idea of a statewide volunteer cybersecurity team has attracted interest from about 15 other states, he said, and there’s been far-off talk of establishing a national network of state teams. If the concept stays on this trajectory, community-based volunteer corps could become a new norm in American cybersecurity.




Leave a Reply
You must be logged in to post a comment.