From Pepsi Bottling Ventures to the American Red Cross, no one is safe from cyber-attacks, as these two organizations are just two in a long list of organizations that have recently dealt with network breaches and the loss of sensitive data.
The private sector isn’t the only target – government agencies are also at risk, and while some have already taken precautions, it’s time for everyone to step up and secure high-value data and applications.
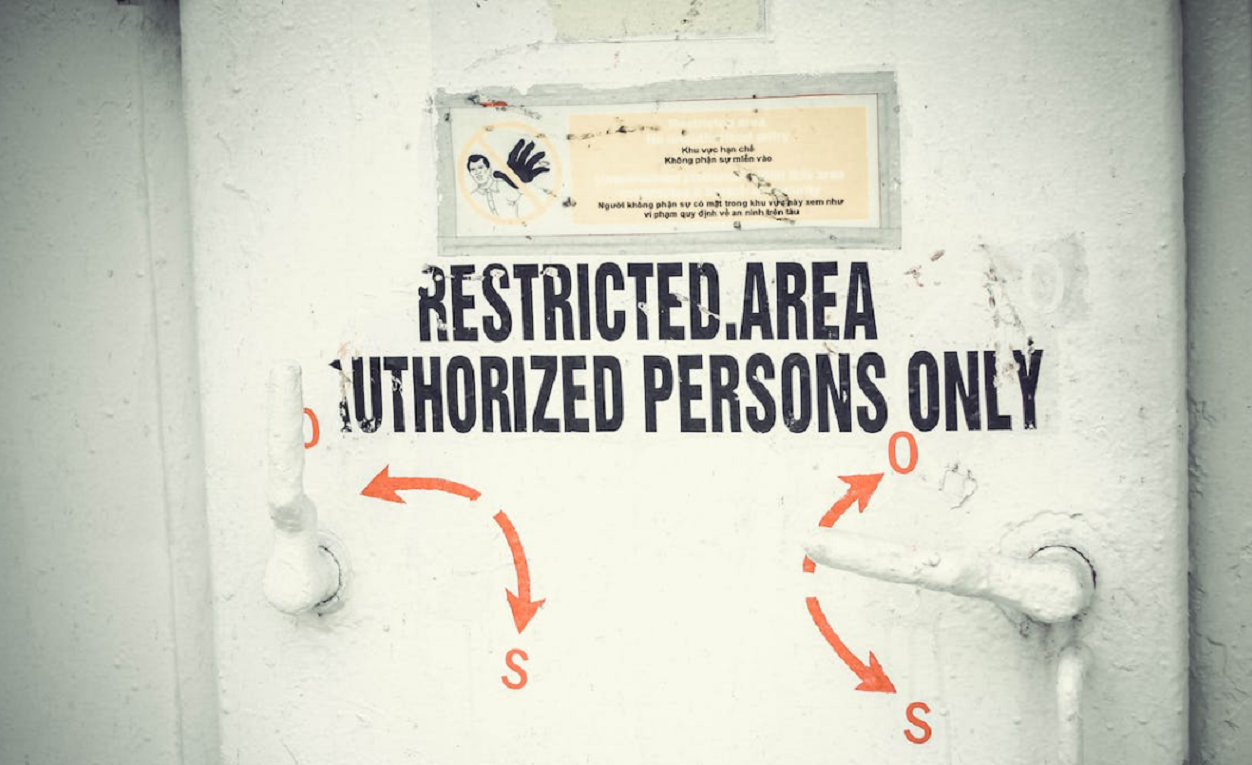
One solution that’s gaining ground is zero trust, a security framework requiring all users to be authenticated, authorized, and continuously validated before being granted access to applications and data. A zero-trust architecture can close existing gaps in security and address new vulnerabilities that have cropped up with an increase in remote work and cloud migration.
Zero trust doesn’t just authenticate users; it also assigns a level of permissions to them, letting them have access to what they need. An example of how this is helpful comes from the U.S. Army Corps of Engineers, who used zero trust to securely share data with external civilian agency customers and partners.
“Our goal is to enable all users that need access to the data … to access it in a more secure manner,” said the Corps’ Chief Information Officer, Dovarius Peoples.
If you’d like to better understand how zero-trust architecture can make your agency more secure while also helping you safely collaborate, take a look at this e-book for practical ideas.




Leave a Reply
You must be logged in to post a comment.