 After my last assignment as the chief information security officer (CISO) for the state of Michigan, I had approximately two weeks of break before my next gig. I had planned an introspection period for a long time, and it was here now. I used this period to think about my successes and failures. I methodically took apart each assignment and listed my successes and failures in terms of initiatives, projects and corporate goals. I also sought feedback from my trusted group of friends, mentors and advisors, who provided their honest and unbiased opinions. This short article discusses my experiences and recommendations for information technology leaders.
After my last assignment as the chief information security officer (CISO) for the state of Michigan, I had approximately two weeks of break before my next gig. I had planned an introspection period for a long time, and it was here now. I used this period to think about my successes and failures. I methodically took apart each assignment and listed my successes and failures in terms of initiatives, projects and corporate goals. I also sought feedback from my trusted group of friends, mentors and advisors, who provided their honest and unbiased opinions. This short article discusses my experiences and recommendations for information technology leaders.
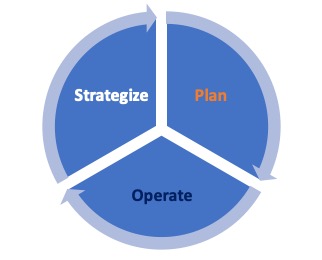
Figure 1: Strategize-plan-operate
Introspection provided me clarity about the following three steps. I found I executed these steps in all the successful initiatives, but they were absent in my failed projects. The three steps were to:
- Strategize
- Plan
- Operate
Let me share some thoughts about these three steps with some examples, which will help you use these recommendations professionally to be successful in your current roles.
Strategize
This is a key initial step. The strategy gets synthesized after conversations with key stakeholders, employees and customers. I have always strived to achieve this within the first 30 to 60 days on the job. This feedback results in identified opportunities, which when merged with corporate goals, provide clarity about the strategy.
It is extremely important to debate the strategy with partners and gain the buy-in for planning. I remember in my last role as CISO, I spent considerable effort in discussing the cyber strategy with my peers such as the chief technology officer and chief information officer (CIO) for alignment.
Plan
Once the strategic alignment is achieved, the goal is to convert the strategy to an actionable plan. A few other things to consider for planning are organizational priorities, immediate pain points to address, environmental issues, resource availability, etc. The plans should be done for a time horizon of 12 to 24 months, in which actions can be executed without too many uncertainties. (The current COVID-19 pandemic is an exception!) The strategy and plan should not be cast in stone. Incremental updates should be allowed to address changing priorities and the changing business environment upon leadership approval.
Operate
The strategy and plan outcomes need to be objectively measured for transparency and trust. Easily adoptable technology platforms are available to measure the plans and should be utilized. Any course corrections required can be funneled back to the strategize and operate functions, as displayed in Figure 1. For my assignments and tenure, I have always operated with near real-time performance dashboards to measure the journey. This also assists with board narrative. Figure 2 below provides a visual representation of sample tools to strategize, plan and operate (SPO).
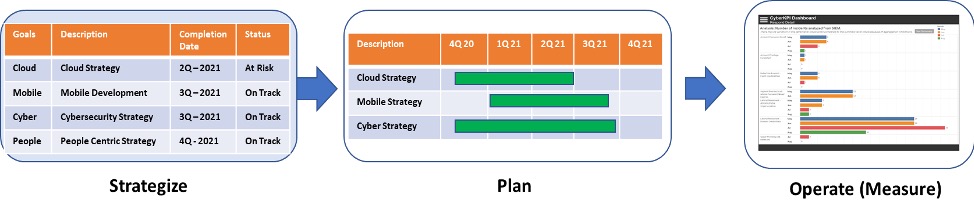
Figure 2: Sample tools for the steps
Recommended reading
I recommend the following books which I have found very helpful in my journey to strategize, plan and operate (SPO):
- Strategy Beyond the Hockey Stick by Chris Bradley, Martin Hirt & Sven Smit (McKinsey & Company)
- Strategy Maps by Robert S. Kaplan and David P. Norton (Harvard Business School Press)
- From Business Strategy to IT Action by Robert J. Benson, Thomas L. Bugnitz & William B. Walton (Wiley)
- Performance Dashboards – Managing, Monitoring and Managing Your Business by Wayne Eckerson (Wiley).
Rajiv has more than 25 years of information technology strategy, operations, large systems integration, cyber security and program management experience. Rajiv is a principal with Plante Moran management Consulting, cybersecurity practice after serving as Chief Information Security Officer (CISO) for the Department of Technology, Management and Budget, State of Michigan.




Very insightful, thanks for sharing!
Thanks.
I love the graphics in this Rajiv! Thanks for sharing your perspective about working for my home state!
Glad to share my experience. Thanks for your guidance and pointers.