Unless you have an advanced degree in cybersecurity, you might be a little confused by all of the techy lingo used to define the threats to government information. How is an advanced persistent threat different from a regular threat? Is phishing what your dad makes you do on camping trips? Isn’t a troll just a mythical beast that lives under bridges? What’s a white hat hacker? Why do hackers need to wear hats at all?
The dictionary for cybersecurity is vast and a little confusing. That’s why we took the time to breakdown the most common types cyberattacks and hackers in our most recent guide, Securing Government: Lessons from the Cyber Frontlines. Our taxonomy is below:
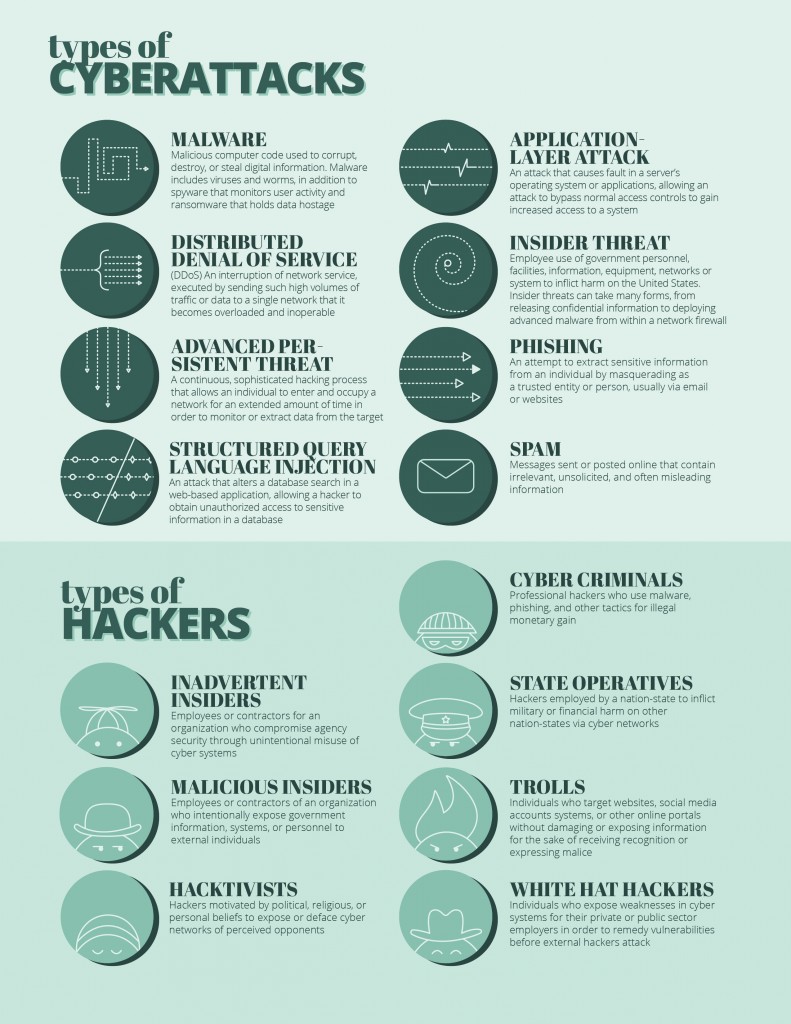
Want to learn more about cybersecurity in government? Be sure to read our guide, Securing Government: Lessons from the Cyber Frontlines, to hear what agencies at the local, state, and federal level are doing to protect government networks from trolls, hactivists, cyber criminals, and more.




Leave a Reply
You must be logged in to post a comment.