If you attended GovLoop’s recent cybersecurity live training in Washington D.C., you know that everybody from folks at the DoD to the FBI were there offering up their thoughts on the new landscape of cybersecurity, and a new mindset. Several of our presenters also talked about important tips and steps folks must take to ensure their data is secure. We compiled several of them below into 20 tips and ways you can make your agency a more secure place.
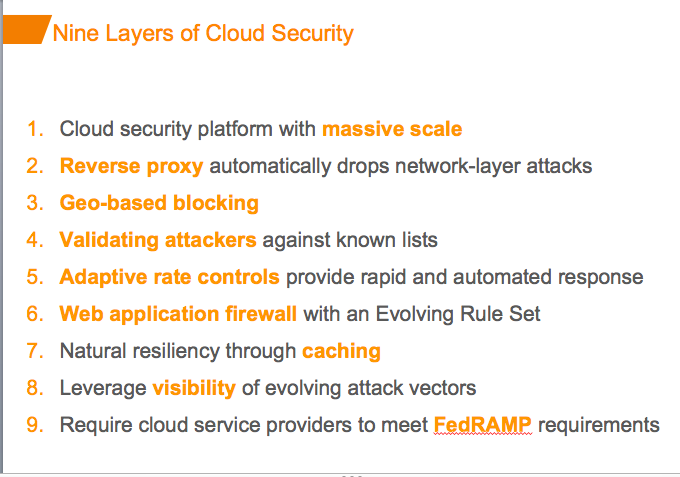
Drew Reinders, Principal Solutions Engineer, Akamai advised organizations they need to avoid becoming the next cyberattack victim in the headlines by making a critical evaluation of cybersecurity practices – and then they must take steps to extend multi-layered security controls to the cloud.
Reinders presented nine important layers of cloud security that must be adapted:
Matt Gildenhorn, Senior Sales Engineer, Public Sector, at Splunk discussed how you can use big data to counteract advanced threats. His plan involved three steps.
- Step 1: Collect ALL The Data in One Location
- Gildenhorn said in order to use big data to detect threats, it all must be stored in one location. Everything from email to databases to call records to network flows should be in one location.
- Step 2: Identify Threat Activity. Gildenhorn explained that this step involves taking a variety of different angles and asking different questions:
- What’s the modus operandi of the attacker? (think like a criminal)
- What/who are the most critical data assets and employees?
- What patterns/correlations of weak-signals in ‘normal’ IT activities would represent ‘abnormal’ activity?
- What in my environment is different/new/changed?
- What is rarely seen or standard deviations off the norm?
- Step 3: Remediate and Automate. Finally, said Gildenhorn, you must ask yourself and do the following:
- Where else in my environment do I see the “Indicators of Compromise” (IOC)
- Remediate infected machines
- Fix weaknesses, including employee education
- Turn IOC into a real-time search for future threats
Next up with Philippe de Raet, Vice President, of Experian, who discussed eight ways the cybersecurity market will be different in less than five years from now.
- The use of ‘data’ as we know today (standard Personal Identifiable Information or “PII”) will be diminished in its value (commodity), and most of the data we use today will have been compromised and posted some place on the internet.
- Authentication services will provide frictionless consumer interaction and allow for multiple levels of security.
- Convergence of security and authentication – clients will want both parts of this equation.
- National Strategy for Trusted Identities in Cyberspace (NSTIC) vision will be created — a single credentialed identity with access to multiple applications across markets and clients.
- Identity as a Service (IDaaS) will be more fully realized across markets and beyond public sector and healthcare. Emphasis will be “context based”; one-size-fits-all approach will no longer be effective.
- Regulatory and other compliance pressures will further restrict PII and client hosted data usage within IAM services.
- Mobile/device based authentication will become the standard as the mobile device becomes the default token credential and may also become the preferred mechanism for registering a biometric.
- Global authentication will become a standard through device + biometrics + location + tokens + social data/behaviors + analytics.
To read more of this forecasting and tips, make sure to see Akamai’s slides here, Splunk’s slides here, and Experian’s slides here.
For more recaps of GovLoop’s recent cybersecurity training, head here.




I am sharing this information with my Team. Keep it coming. Excellent. Thank you, David