 In 2014, Congress passed the Federal IT Acquisition Reform Act – commonly referred to as FITARA – to help federal agencies reduce IT waste, improve how IT is purchased and managed, and drive technology reform across all federal agencies. Not only was FITARA a game-changer – altering the way that the government thinks about federal IT, but it also represented the first significant revamp of Federal IT in over 20 years.
In 2014, Congress passed the Federal IT Acquisition Reform Act – commonly referred to as FITARA – to help federal agencies reduce IT waste, improve how IT is purchased and managed, and drive technology reform across all federal agencies. Not only was FITARA a game-changer – altering the way that the government thinks about federal IT, but it also represented the first significant revamp of Federal IT in over 20 years.
One of the most important pieces of the legislation is the annual FITARA Scorecard that grades agencies on how well they are doing. For this blog post, I collaborated with Curt Cote, a Partner at Censeo and recognized leader in Federal Category Management, to share his expertise on how agencies can make improvements to their scorecard.
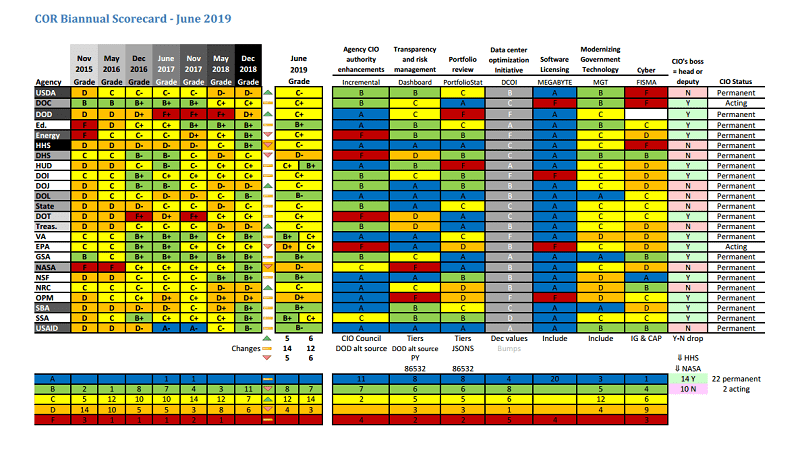
The House Oversight and Reform Committee’s latest scorecard 8.0 released in June 2019, reveals that although the 24 largest Federal agencies are making progress on critical initiatives since the first release back in 2015, there is much work left to be done. Although no agency received a failing grade, only 7 agencies received a score higher than a B-, indicating that every agency has room for improvement. Considering that FITARA is now the standard by which agencies are being graded on their use and implementation of software license management, CIO reporting structure, cybersecurity sand IT governance, agencies should be investing time and resources into the right categories to boost their overall score.
With this in mind, we believe that the scorecard results reveal an opportunity for significant improvement in two categories in particular: Risk Management and Data Center Consolidation. Next week, we will do the same with a focus on lessons learned and success factors around effective Data Center Consolidation strategies.
3 Key Next Steps for Risk Management
OMB’s IT Dashboard section of the scorecard is designed to measure if agencies are monitoring and acknowledging project risks by tracking the percentage of significant IT investments for which agencies have completed and reported risk assessments. So, how can you increase this transparency for your agency?
Step 1: Develop a Risk Assessment Methodology
In order to mitigate risks, it’s important to understand what projects are in your pipeline and what the potential risks are with each. When creating a methodology to assess project risks, be sure to:
- Catalog Your Projects: Develop a central repository or dashboard of current and planned IT investments/projects. Tracking risks on all projects (major & minor) is a standard commercial best practice and is the critical first step of any risk management plan.
- Gather Input to Define Risks: Use your internal stakeholders and external subject matter experts to identify the potential risks, both observable and hidden, on each project. Start with a manageable list by focusing on the indicators that arise when a project is going off track. Then, compile this information into a centralized list for future use.
- Involve the GAO: Your score is partially dependent on the degree to which GAO understands and accepts your methodology. To increase your transparency, schedule a time with GAO to review your process.
Step 2: Create a Straightforward Risk Rating Process
The next step is to create a tangible, sustainable system for assessing each project in your dashboard. The following steps can help you to create a consistent, easy-to-follow measurement process that can quickly identify when a project is at risk:
- Focus on Key Indicators: Start simple and just focus on these 3 key indicators: the severity of the risk, the probability of the risk, and your organizational readiness to react should the risk manifest. Don’t add additional costly reporting requirements for things that don’t matter.
- Document Decisions: Maintain a record of why you rated project risks as you did and the data you used to make your decision. You’ll be glad to have this traceability if the project is audited in the future.
Step 3: Aggregate & Report Risks
The last element of your grade will be based on your ability to document and track risks identified within projects. Take these following steps to ensure transparent results:
- Aggregate Results: Compile your risks across projects into the form required for the IT dashboard. If you aggregate multiple projects into a single entry on your dashboard, be sure you’ve documented your approach to aggregation.
- Utilize a Manageable Reporting Process: Since risks need to be measured and reported monthly, invest some time in building a process and the tools to make risk assessment and reporting easy. A common pitfall is making the process too complex by trying to manage and report too much.
- Report to OMB: This step is essential since the FITARA grade is based on what you report to the IT dashboard. Implementing a monthly cadence of reporting your data will ensure that you are meeting deadlines and that your FITARA score will be an accurate reflection of your efforts.
Conclusion:
By taking these steps, your organization will not only improve your Dashboard grade on the FITARA scorecard, but you’ll also improve your ability to mitigate risks across your IT projects. Identifying risks early can save both time and money while keeping your agency out of the headlines.
In next week’s blog post we will go over the best practices for Data Center Consolidation to ensure that your agency is allocating the time and resources to the other focal category and ultimately ensuring that your agency gets the grade.
You may also be interested in the previous blog post that I collaborated with Curt Cote on, Pushing Category Management Forward: 4 Practical Next Steps
Derrick Moreira, President of Censeo Consulting Group, has more than 22 years of management consulting and industry experience leading and delivering complex supply chain and operations strategy solutions. Most recently, Derrick has played a key role in standing up and managing several large-scale supply management transformational initiatives across federal agencies. Key areas of subject-matter expertise include supply management and strategic sourcing, cost and business case analysis, workforce planning, program governance, change management, and process improvement/ reengineering. You can read his posts here.



Leave a Reply
You must be logged in to post a comment.