There is no shortage of information on the interwebs about the massive Office of Personnel and Management breach that left computer systems and data exposed to hackers.
The hard part is cutting through the jargon and speculation to understand what happened and what this hack means for you, especially if you’re one of the 4 million current and former feds whose personal data may have been compromised. Sorry to be the bearer of bad news, but as OPM’s investigation of the incident continues, there’s a possibility that number could grow. (Read our most recent coverage here).
“Since the investigation is on-going, additional PII exposures may come to light; in that case, OPM will conduct additional notifications as necessary,” OPM said in a recent Q&A.
According to the agency’s timeline, OPM’s systems were breached in December 2014. OPM became aware of the cyber intrusion in April, only after it beefed up internal security measures to detect and mitigate cyber attacks. A joint investigation with the FBI and Department of Homeland Security’s US-CERT revealed last month that personal data may have been stolen. How the attack occurred and who was behind it are still under investigation, but reports citing unnamed U.S. officials claim that China is the perpetrator.
Because there are still a lot of maybes and ifs swirling around this incident, we wanted to do our best to distinguish between the facts, speculation and what details are being fleshed out – and what all of this means for you. Let’s start with the burning questions:
#1: Who was affected?
The breach may have compromised personal data of 4 million current and former federal civilian employees at executive branch agencies, including the Department of Defense. Military records were not affected. Contractors are off the hook, too, unless they are former federal employees. OPM said that family members included in your records were not affected by the breach.
#2: What does this hack mean for me?
If your information may have been compromised, you will be notified by OPM over the next two weeks. Notifications started going out on Monday, June 8, and will continue through June 19. “The communication to potentially affected individuals will state exactly what information may have been compromised,” OPM Press Secretary Samuel Schumach told GovLoop. Personal data that may have been stolen include:
- Names
- Social Security numbers
- Birthdates, place of birth
- Current and former addresses
- Job assignments
- Training records
- Benefit selections
“At this time, we have no evidence that there has been any use or attempted use of the information compromised in this incident,” OPM noted. But it isn’t uncommon for hackers to sit on information for months — or even years — before carrying out malicious acts.
#3: Is this one of the worst breaches in government history?
“This was the most significant breach of federal networks in U.S. history,” Rep. Michael McCaul, Chairman of the House Homeland Security Committee, said on CBS’ “Face the Nation.”
McCaul called the breach a huge data-mining project that appears to be the work of the Chinese government. “It was not done to steal credit card information, it was done to get personal information on political appointees and federal employees,” McCaul said.
For now, we know that as many as 4 million current and former feds may have had their records compromised. “What we don’t know is the degree,” said Steven Spano, President and Chief Operating Officer of the Center for Internet Security.
Spano recalled the 2006 theft of a Veterans Affairs Department employee’s laptop. The laptop contained personal information of about 26 million veterans and military personnel, which far surpasses the 4 million potentially affected by the OPM breach. But the number of potential victims isn’t the only indicator for determining the impact of a breach. “The question is what type of information was breached within those records,” Spano said.
#4: What if I get a notification that my data could be at risk?
“This may or may not go without saying, but you should be leery of any emails that contain links and attachments and claim to be about the OPM breach,” said Dan Waddell, Director of Government Affairs for the nonprofit security organization ISC2. “Do not treat this as your standard after-breach process, where you sign up for credit monitoring and think everything is okay,” Waddell said. “You need to be on the lookout for targeted spear-phishing attacks.”
Now that cybersecurity is going mainstream, you’ve probably heard of the term spear phishing. This tactic includes targeted attempts, usually via email, to extract sensitive information from an individual by posing as a trusted entity or person. One concern is that hackers may use stolen data about federal employees to trick them into opening malicious emails. One click could provide adversaries an open door into your agency’s network.
The domino effects may not be felt in the coming months — but years, according to security experts, who fear that hackers could use personnel data to target individuals working on sensitive projects and those who may be more susceptible to bribes and coercion due to financial hardships or other life issues.
If you have a security clearance, then you know the type of sensitive information that must be reported to the government. Think of this information as the “data people sometimes freely put on LinkedIn but on steroids — information that you wouldn’t want publicized,” said Ryan Kazanciyan, Chief Security Architect at Tanium. The firm was dubbed by Forbes as the secret cybersecurity weapon of Target, VISA and Amazon
#5: What services are available for affected individuals?
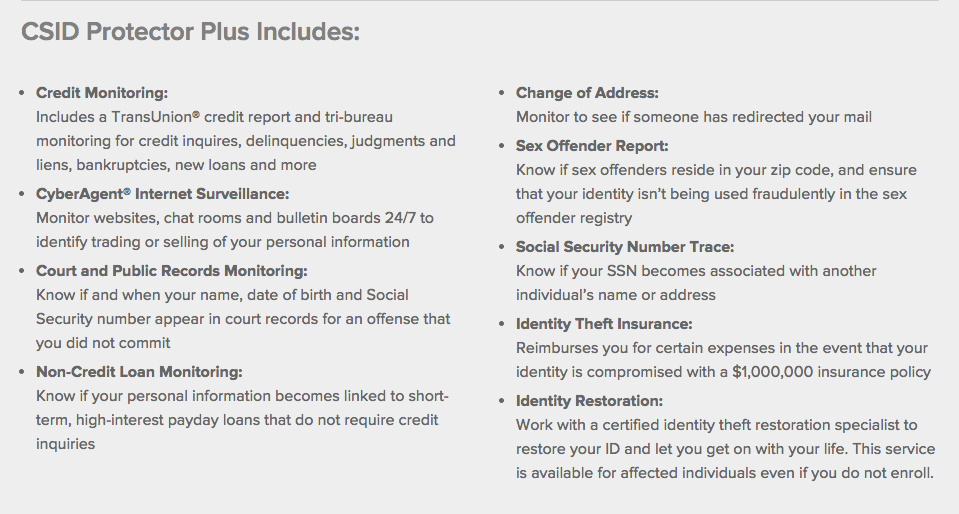
OPM is giving affected individuals a free subscription to CSID Protector Plus for 18 months. Check out the chart below to see what’s included in the coverage for those who enroll. Affected individuals will automatically receive $1 million of identity theft insurance and full-service identity restoration provided by CSID, OPM noted.
#6: If OPM discovered the breach in April, why are feds just now hearing about it?
Let’s revisit the timeline I provided earlier: OPM discovered the breach in April, but it wasn’t until May that the agency found out personal data may have been compromised. “As with any such event, it takes time to conduct a thorough investigation and to identify the affected individuals,” OPM said.
Tanium’s Kazanciyan agrees.
“For an organization that has been compromised there is always strong forces driving them to disclose as early as possible with as much information as possible,” said Kazanciyan. His past experience at security firm Mandiant included leading investigations into targeted attacks and helping companies detect and respond to them. “The challenge is these types of investigations often take time,” and organizations are often compelled to give information before they understand the full extent of the breach. That’s why some organizations end up revising early estimates about the impact of a breach — not because they tried to withhold data but because the investigation is ongoing.
Some breaches can be determined in a matter of days or weeks, if the right security tools are used and experienced professionals are involved, Kazanciyan said. He has seen some cases where the investigation takes months or years, only to yield insufficient details for remediating problems.
#7: What is OPM doing to secure itself?
The federal government as a whole has been implementing a DHS program known as Continuous Diagnostics and Mitigation. I promised I wouldn’t throw around too much jargon, so I’m going to keep it simple: The $6 billon program was created to give agencies access to standard software tools and services. Using these software tools, agencies can conduct automatic security checks of their network to see what devices are connected to their computer networks, if those devices have updated software patches and check a host of other potential security risks.
Following the breach, OPM implemented several new security measures, including restricting the access of network administrators who are remote, clamping down on the functions of remote network administrator and rolling out anti-malware software. But why did it take a cyber intrusion of this magnitude to spur improved security?
OPM isn’t the only government agency slow to respond to the increasing cyber threat, as noted in the annual information security report to Congress. That’s only part of the problem.
“A lot of security in the government is still driven on the front end by compliance,” Kazanciyan said. And compliance with a list of security standards, while good for maintaining cyber hygiene, is not the same as constantly monitoring federal networks for signs of a breach.
#8: What is the EINSTEIN program that was used to detect OPM breach?
EINSTEIN is a system created to detect and prevent intrusions of federal networks. DHS is working with agencies to implement the most updated version, known as EINSTEIN 3 Accelerated (E3A), government-wide.
At an April 15 Senate subcommittee hearing, Andy Ozment, Assistant Secretary for DHS’ Office of Cybersecurity & Communications, called EINSTEIN 3 “a first line of defense against cyber threats for federal civilian departments and agencies. E3A can be considered a set of security gates on the federal government’s traffic, located at the handful of Internet Service Providers (ISPs) that are used by almost every federal civilian agency to access the Internet.” The tool offers several features, including an email filtering capability that allows DHS to scan email destined for .gov networks for malicious attachments and other malware.
“Currently, approximately 26 percent of Federal civilian personnel are protected by at least one of E3A’s capabilities,” Ozment said at the hearing. As of April 3, a total of 51 agencies had signed agreements to roll out the services, which would raise EINSTEIN 3 coverage to 96 percent of all federal civilian personnel.
The OPM breach has accelerated rollout of the DHS program, which was initially scheduled to be adopted government-wide in 2018, White House Press Secretary Josh Earnest said at a June 5 briefing. That timeframe has been bumped up to 2016.
One drawback is that intrusion detection systems like EINSTEIN rely on unique identifiers, or signatures, to detect cyber threats that are known but does little to find unknown threats, said Kazanciyan.
#9: This isn’t the first time OPM has been hacked, right?
Correct. Last year, it was reported that hackers gained access to OPM databases, in addition to attacks against agency contractors.
This most recent OPM cyber hack may seem like déjà vu for more than 40,000 employees who were notified by the agency in December that personal data may have been compromised, following an attack against OPM contractor KeyPoint Government Solution. The company became OPM’s go-to background investigations firm after competitor U.S. Investigative Services fell victim to a cyber attack and lost its contract.
The nature and target of these attacks are not a coincidence, Kazanciyan said.
“To me, this is clearly a situation where an attacker deliberately targeted PII (personally identifiable information), including data on background investigations and the other data that OPM collects as part of its role in the government, for the purpose of intelligence collection on government employees,” he explained. “I would distinguish that from more common stealing of PII to commit fraud.”
#10: What should I do to protect myself?
OPM offers a host of tips for current and former federal employees. Here are a few:
- You may place a fraud alert on your credit file to let creditors know to contact you before opening a new account in your name. Simply call TransUnion at 1-800-680-7289 to place this alert. TransUnion will then notify the other two credit bureaus on your behalf.
- Be suspicious of unsolicited phone calls, visits, or email messages from individuals asking about employees or other internal information. If an unknown individual claims to be from a legitimate organization, try to verify his or her identity directly with the company.
- Pay attention to the URL of a website. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain
- If you are unsure whether an email request is legitimate, try to verify it by contacting the company directly. Do not use contact information provided on a website connected to the request; instead, check previous statements for contact information.
#11: Should state governments be concerned?
Erik Avakian, Pennsylvania’s Chief Information Security Office, said he is keeping a close eye on the OPM incident, specifically what information was compromised, what security measures were in place and how information may have been compromised. All the specifics likely won’t be released publicly, but states such as Pennsylvania have mechanisms for sharing and receiving more sensitive information with its partners.
#12: Where can I get more information?
For information pertaining to the incident and your coverage, OPM is directing individuals to visit www.csid.com/opm, or call 1- 844-222-2743.
If you have additional information that would be helpful for former and current feds to know, please include it in the comments section.
Related Links:




Have received two emails from blue cross blue shield, since January. We did not enroll with bcbs , and they should not have my email. I did not open these emails. I was uncomfortable, and wondered how they got the address. OMP does have this address.
You did the right thing. If something seems fishy, it’s better to play it safe. If you want to follow up, you can always reach out to Blue Cross Blue Shield via phone and find out what’s going on and if the email is legitimate.
This damage may well be catastrophic. Why hasn’t the incompetent leadership (i.e. CIO Donna Seymour or Security Chief Jeff Wagner) been sanctioned or better yet fired?
I second that. Seymour is blatantly unqualified and has been hiring her obviously incompetent cronies at a time when information security is critical and requires exceptional education, experience, and leadership.
I agree with Henry. The CIO spent money on building her kingdom instead of prioritizing work on cyber security. It is a pity she put her friends and or leaders who have no leadership experience in positions rather than giving those already in her organization opportunity who have the expertise!!!!
Seymour doesn’t follow OPM hiring best practices, she puts people in position who have no ability to lead. Irresponsible.
I would like proof of breach as CSID is a contractor and is wanting me to put all eggs per se’ in one basket and after reading the privacy act they can sell the information and transfer internationally as well as use sub-contractors to perform the surveillance. Although I did have a fraudulent incident last November that involved a credit card and an Airport, I am still leery of putting everything there in one place on CSID. We trusted OPM, what’s to say the contractor they hired will do better. I feel that it all should be handed over to DOD Cyber for the most trusted resolution.
This point to the stupidity of storing all data in one place. One attack gets all data. The federal government is a mass of idiots, slackers and incompetents. DC is one big useless pile of dung!
And how did affirmative action hiring by government agencies play into this? They are being paid like competent people but they are not competent.
DoD isn’t the answer-those at OPM are former DoD – the head of investigations is a former intelligence officer. I am not impressed with their ability. Learning from this and ensuring the agencies all have money to tighten the holes is needed not current Congress and Senate slashing budget – you cut budgets to bare bones and you get what you pay for.
Gee, thanks, Margaret. We’ll send the bill to blow out the budget to your home address. So glad you are rolling in the benjamins and can foot the bill.
(Hint: The money doesn’t multiply and divide on its own; we need a functional economy before we add more charges to the national credit card. I take it you don’t budget very well in your personal life.)
Crowley – I am a taxpayer same as you. Secondly, DoD’s budget is over inflated, always has been; better cross agency allocation based on sound strategy and planning. I also agree with MCS – hiring Sr. IT PMs is not the answer and is a waste.
[…] are not a rare occurrence. However, events like the OPM hack have brought cybersecurity to the forefront of many federal CIOs’ concerns. Survey results […]
[…] the wake of OPM’s June 4 announcement that some 4 million people were affected by the cyber hack, new reports have surfaced that create […]
[…] GovLoop reported last week that OPM’s systems were breached in December 2014. OPM became aware of the cyber intrusion in April, only after it beefed up internal security measures to detect and mitigate cyber attacks. A joint investigation with the FBI and Department of Homeland Security’s US-CERT revealed last month that personal data was compromised. How the attack occurred and who was behind it are still under investigation, but reports citing unnamed U.S. officials claim that China is the perpetrator. […]
In the letter from CSID they say something like those who were breached are covered for fraud and identity theft with insurance whether we enroll with CSID or not. So, I don’t have to enroll on their site for that coverage then, right? It sounds like I am automatically covered. I mean, they ask for your ssn and personal info on there, and I don’t want to give that out.
Hello. Were you able to sign up for coverage? I was told that you are not automatically enrolled and will need to sign up for coverage using the PIN code that was sent to you, as well as your SS number. I know that’s less than ideal, but it seems there is no way to get around it if you want coverage.
I believe that from the letter I received…you have two choices, either by contacting them every time per each incident basis (or) enrolling with them as a subscriber which means providing them with your personal information, billing, etc.
I’m a retired Federal employee and I haven’t heard a peep out of OPM and they have my contact information. I can’t trust that my data hasn’t been compromised just because I haven’t heard anything from them. I wrote them an email asking if my data was one of the one’s compromised, but I haven’t heard a peep back from them. Any suggestions?
Hi Art, if you were one of the 4.2 million affected by the first breach you should have received notification by now. The second batch of notifications for the affected 21.5 million people will be going out in the coming weeks. OPM is setting up a call center to field questions, and I highly recommending calling once that information becomes available. Feel free to email me directly, and I can see what I can do to help. [email protected]
Quick question (looking to follow up on family member’s notification)
Post sign-up on their website, Is CSID sending out insurance papers electronically and requesting a 0.27 a month premium for the services?
Thanks,
Terry
[…] today than were dealing with it before. Not sure what we’re talking about? Find out more here. A data breach doesn’t necessarily mean that everyone’s identity will be misused tomorrow. For […]
I know they are giving us free credit protection for the next 2 years but what about after that. when people take your identity they wait for two to three years to sell it. they have finger prints and family members info and medical records and background check information this can potentially affect all our lively hood for the rest of our existing life. how is the government being held accountable for that and will they come to our rescue when that day happens to us and we are in trouble because of someone else miss use of our information?
Hi Sam, that’s a a serious concern for everyone impacted by the breaches. OPM said it will consider credit and identity theft monitoring services that should be provided to all federal employees in the future – regardless of whether they were affected by the breaches. How long those services would be provided is the question…
Anyone who has a disability and uses assistive technology is, for now at least, screwed further. The site isn’t accessibility, enough though CSID is obligated to deliver a Section 508-conformant product. It was a two-day turn-around product, from contract signature to delivery, so they didn’t bother/couldn’t include accessibility/Section 508-conformance.
the video from a month ago (https://youtu.be/Vh_rAu3-Gb8) still hasn’t been fixed. It shouldn’t have even been released if it was inaccessible. It still hasn’t been made accessible to either persons who are Deaf (captioning) or persons who are blind (audio-described).
All the information hacked has got to compromise every person with a clearance working CONUS and OCONUS. It will be easy to check everyone going to and leaving any country who has this information.
This should be an “Act of War” because this compromises everything personal, private and secret, EVERYTHING!
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the OPM hack back in June, few understood the massive scale of the attack. Originally thought to have affected 4 million […]
[…] news first broke of the U.S. Office of Personnel Management(OPM) hack back in June, few understood the massive scale of the attack. Originally thought to have affected four million […]
[…] news first broke of the U.S. Office of Personnel Management(OPM) hack back in June, few understood the massive scale of the attack. Originally thought to have affected four million […]
[…] news first broke of the U.S. Office of Personnel Management(OPM) hack back in June, few understood the massive scale of the attack. Originally thought to have affected four million […]
[…] news first broke of the U.S. Office of Personnel Management(OPM) hack back in June, few understood the massive scale of the attack. Originally thought to have affected four million […]
[…] news first broke of the U.S. Office of Personnel Management(OPM) hack back in June, few understood the massive scale of the attack. Originally thought to have affected four million […]
[…] news first broke of the U.S. Office of Personnel Management(OPM) hack back in June, few understood the massive scale of the attack. Originally thought to have affected four million […]
[…] news first broke of the U.S. Office of Personnel Management(OPM) hack back in June, few understood the massive scale of the attack. Originally thought to have affected four million […]
[…] https://www.govloop.com/12-things-you-should-know-about-the-opm-breach/ […]
This information doesn’t jive with the letter I just received from the OPM (or at least that’s what it says it is). IN that letter they’re using a services called ID Experts and offering 3 years of protection services for employees and their children (but not their spouses even though the letter specifically states that a spouse of an employee may have been compromised if the employee listed any of their information on a background check form. Which one is the correct information?
This story is about the first breach. Based on the fact that you received a letter from ID Experts, that means you were impacted by the second breach. You’re correct, spouses were also impacted in the second breach. According to the OPM site, there is credit monitoring offered for those affected spouses. See this link: https://www.opm.gov/cybersecurity/cybersecurity-incidents/. But you’re saying that is not the case. I’m more than happy to chat with you offline to help you sort things out. You can reach me directly: [email protected]
My info was stolen due to this . I feel like I can’t trust our government now … I’m getting a lawyer and filing a lawsuit … There should have been better systems to keep this info from being stolen … Since its not the first time
have you contacted a lawyer? I’m thinking the same thing, it has ALL MY INFO and my kids ssn. what did the lawyer say?
I think the Federal Government should have to protect ALL 22 million of us…..they have all our information…so protect us….why should we have to do it???????????
Tried to create an account, but will not accept the street address…what do I do???
I would reach out directly to the contractor providing the monitoring services on behalf of OPM. I’m not sure whether you were affected by the first or second breach. If you were among the 21.5 million affected, here are some tips on registering for services https://www.govloop.com/advice-for-the-21-5-million-opm-hack-victims/
Nicole, this service is absolutely the most useless service in existence. You need something like lifelock. The OPM has gone too far and deserves to be abolished. They have cost many lives whether financially or physically. Imagine all of the agents they have put in dangers by leaking top secret information. The OPM is in violation of national security and should have NO DAMNED ROLE in investigating any employee. I will not be participating in these investigations until the OPM is no longer part of them.
I think when it comes to the federal hiring process, each agency should be in charge with the actual hiring, not OPM. OPM should not have any authority in the process. One organization overseeing the majority of the federal hiring process is to much to take in. By giving the hiring authority to each agency it would take a lot of pressure off OPM and even save money. Plus, OPM is terrible with investigations when it comes to employers. For some reason in today’s society, employers are so vindictive and vengeful that they will lie like hell just to ruin your life for outing their corrupt activities and just simply doing the right thing. One person (Mr. M) looking to work for Immigration found out that their former employer told OPM investigators that they fired him because Mr. M cursed out their boss. Not only was this a lie, but it was in violation of the U.S. Privacy Act of 1974.
When Mr. M found out what was said in the investigation they took their former employer to court and won and it wound up embarrassing OPM because the investigators were subpoenaed into court. The investigators were asked by the plaintiffs attorney why the investigators ignored the former employees who informed them that Mr. M was fired for the wrong reasons. The attorney asked why investigators did not take into account that the other former employees said that the employer lied about the reason for firing Mr. M and that the employer has problems that creates mistrust in the public eye. The former employees told investigators that Mr. M is an outstanding citizen who does the right thing and the true reason for his firing was that Mr. M’s supervisor wanted him to mess with insurance prices and other information that would con the elderly to pay more money. Mr. M knew this was illegal and immoral and refused to do it because he could get into serious trouble. So the supervisor fired him. Even though investigators could not find any evidence showing that the supervisor wanted Mr. M to con the elderly, they believed the supervisor and chose not to hire Mr. M. The former employer hid the real reason for firing Mr. M and that was even told to investigators by former employees.
The jury took into account the problems this company was having and the stories of the other former employees. Mr. M won the case and was awarded thousands of dollars in damages. The hiring authority of OPM looked like an accomplice to the villainy of the former employer because they chose not to hire Mr. M because he was fired.
Another reason why Mr. M won the case was because whether or not the former employer lied, they still violated the U.S. Privacy Act of 1974. Investigators should not be asking information that violates the privacy act and the former employer should not be giving out any information. Therefore both the former employer and OPM were in the wrong. Below is the U.S. Privacy Act of 1974 which can be found on the U.S. Department of Justice’s website.
The “No Disclosure Without Consent” Rule
“No agency shall disclose any record which is contained in a system of records by any means of communication to any person, or to another agency, except pursuant to a written request by, or with the prior written consent of, the individual to whom the record pertains [subject to 12 exceptions].” 5 U.S.C. § 552a(b).
The rest of the act can be read at https://www.justice.gov/opcl/conditions-disclosure-third-parties
What is being done if data may have been lost or thru deleting sensitive info on ur personal computer to include IRS past returns and now being audited by the IRS? Data such as mileage / expenses. Any exceptions from OPM and or from Congress to excempt affected individual from IRS audits by those affected by this breach of trust. This is a nitemare/ or has Congress passed some provision(s) to exclude those persons that have been notified that they have been hacked and if not why not? Would OPM suggest I should go see my congressmen and/or Senator. I will do so since I use to work on the Hill on the Senate side and am familiar with the protocols. I would very much appreciate a reply and thank you for your efforts.
During the week of July 24, 2016 four people in my office at the Memphis VA had Amazon Visa cards opened through Chase. None of them applied for or authorized this. To much of a coincidence. Guess our information is out there for al. Thanks OPM
[…] a crucial role in providing a defensive layer to protect networks from breaches. Case in point, the attack upon the Office of Personnel Management that exposed more than 21 million personnel records. The use of smart cards could have perhaps […]