Make Your Data Future-Ready
Government agencies need better data management to keep up with growing demands in cybersecurity, analytics, and artificial intelligence. But how can they do that without slowing down innovation? Can stronger data governance lead to smarter, faster decisions and more efficient operations? These questions were the focus of a recent GovLoop virtual event, “Future-Proofing Your DataRead… Read more »
4 Ways to Shift to People-Centric Security
Good cybersecurity has two basic components: the technology itself and the people and processes that put it into practice. Unfortunately, many cybersecurity programs tend to focus on technical problems and lose sight of the human element. In this takeaway resource, Ralph Hogaboom, Chief Information Security Officer at Washington’s Department of Natural Resources, shares insights onRead… Read more »
How Federal Health Agencies Can Step Up Their Cyber Defenses
Healthcare is under siege — ransomware, identity theft and medical device vulnerabilities are rising fast. In this resource, you’ll explore how an integrated, automated platform approach can help healthcare agencies identify threats, assess potential impacts, and mitigate risk. You’ll learn more about: How technological and organizational issues can hinder the effectiveness of traditional cyber defense strategies. CurrentRead… Read more »
How to Verify Identities in a Complex Data Landscape
Government agencies must accurately identify people and organizations to deliver benefits, prevent fraud and enforce sanctions. But inconsistent formats, language barriers and hidden identities make it challenging. This resource explores how entity resolution (ER) software helps agencies pinpoint identities in real time. You’ll learn: Why identity matching is harder than it looks. What makes ERRead… Read more »
Implementing AI to Combat Fraud and Abuse
Organized fraud rings are increasingly coordinating attacks on benefit programs built on outdated systems to siphon away billions of dollars. These attacks not only divert funds away from program objectives but can also deprive legitimate recipients of their benefits. Luckily, AI and machine learning (ML) have demonstrated value in modeling potential attacks, making them easierRead… Read more »
4 Ways to Make the Most of AI in Cybersecurity
Agencies are discovering that cybersecurity strategies that worked even a few weeks ago might be nearly obsolete today. One approach that is taking hold, however, is the use of AI. In a recent GovLoop online training, experts highlighted four ways that security teams can make the most of AI, including modernizing their identity-based security to integrate AI.Read… Read more »
6 Cyber Focus Areas for 2025
In this quick resource, you’ll get advice on where your agency should focus its cybersecurity efforts.
How to Strengthen Your Ransomware Defense
With approximately 75% of respondents in a recent worldwide survey saying they’ve experienced ransomware attacks in the last year, it’s clear that this type of risk remains a constant threat. So, what can be done to prepare for or prevent ransomware attacks? During a recent GovLoop virtual event, government and industry speakers discussed tips forRead… Read more »
AI and Cybersecurity: Working With the ‘Known Unknowns’
As agencies grow more familiar with artificial intelligence (AI), they see its cybersecurity implications more clearly. Based on discussions at a recent GovLoop roundtable, this resource highlights perspectives from government and industry experts on the most critical cybersecurity and AI challenges. Gain insights from: Taka Ariga, Chief Data Officer, Acting Chief AI Officer, Director ofRead… Read more »
How Federal Agencies Can Fuel Innovation With a Secure Digital Ecosystem
Federal agencies cannot discuss innovation without also talking about cybersecurity. That has never been more apparent than it is today, as agencies accelerate their adoption of cloud and artificial intelligence solutions, each of which presents challenges and opportunities for agency security teams. In this quick resource, you’ll learn how federal agencies can drive innovation whileRead… Read more »
6 Tips for Cybersecurity Compliance
Compliance is not easy. Agencies must prove that they’ve implemented the right security controls and that they’re continuously monitoring them. How can they do it all? This quick, two-page resource outlines six best practices for agencies looking to evaluate their cybersecurity efforts while demonstrating compliance. Download your free copy now: Brought to you by:
Elevate Cyber to Support the Mission
Cybersecurity leaders need to go beyond mere compliance – the cyber defense bar should be set higher. Agencies should lock down their data in ways that keep it safe, while still making it readily available across organizational silos. This quick resource offers tips and takeaways from government and industry experts on how to best protectRead… Read more »
7 Ways to Sharpen Your Cyber-Focus
Cyber experts emphasize the rising threat of ransomware and other malicious activities, driven by well-funded cybercriminal groups and nation-state actors. They predict that AI will enhance attackers’ capabilities and adaptability, posing challenges for government agencies with limited budgets. Michael Gregg, CISO of North Dakota, highlighted these concerns at a recent GovLoop Virtual Summit on cybersecurityRead… Read more »
How to Rise to the Challenges of Data Protection
Agencies are facing numerous challenges around data protection – some you can control and some you can’t. However, there are steps you can take to strengthen your defenses, despite how treacherous the threat landscape may seem. This quick resource offers takeaways from a recent roundtable discussion and includes strategies for leveling up data protection. You’llRead… Read more »
Why Better Security Requires More Than Better Tech
Good cybersecurity requires more than just good security solutions. To deal with the increasing velocity of attacks, agencies must look beyond individual products and think in more holistic terms: looking at policies, processes and even communication strategies. That was the focus of a recent GovLoop digital event, Zero Trust at the State and Local Level,Read… Read more »
How to Keep Your Bearings in Today’s Threat Landscape
Government has been driving toward zero trust-based cybersecurity methodologies for the past couple years. Download this quick resource to see what advice government and industry experts have to offer on the current threat landscape to help shape your cyber agenda for 2024. You’ll learn: Key cyber threats to monitor closely. Proactive security efforts you shouldRead… Read more »
How to Take the Friction Out of Cloud Security
Risks are everywhere in the cloud, and with agencies across the board struggling to manage the vast number of tools they have within their cloud environments, a better, stronger approach is needed. Download this quick resource to discover why organizations should turn to a single cloud-native application protection platform (CNAPP) to protect users and dataRead… Read more »
7 Cyber Areas That Deserve Your Attention
Many IT leaders are using limited resources to maintain their agency’s defenses and put out fires. And all of this is happening as government continues shifting toward a hybrid work environment, which requires fresh thinking about cyber strategies. This resource features tips to navigate this complex cybersecurity landscape, with advice from cyber thought leaders including:Read… Read more »
Navigating the Zero Trust Journey
Zero trust is not a product. It’s a mindset, an architecture and a methodology to follow over time to secure your agency’s systems. Download this quick resource to learn where to start and what needs to be done first when it comes to zero trust implementation to meet the basic tenets and requirements for thisRead… Read more »
5 Best Practices Adopted by Cyber-Savvy Teams
In many organizations, cybersecurity is often treated as a compliance to-do. But in order to bring lasting change, agencies need to create a more cyber-literate culture. This short, overview resource highlights takeaways from a recent discussion with government experts about how agencies can help employees work both effectively and securely. You’ll explore insights from: Kirk H.Read… Read more »
How to Embrace Code-to-Cloud Security
As government agencies continue to leverage the benefits of cloud, the task of meeting security, governance and compliance requirements becomes increasingly critical. This new topic snapshot report provides a concise overview of the challenges agencies face as well as solutions to those problems. You’ll also explore five best practices for implementing a code-to-cloud model toRead… Read more »
6 Ways to Close Your Organization’s Cyber Gaps
The stakes just keep getting higher when it comes to cybersecurity. A government agency is hit with a ransomware attack every 14 seconds, according to a recent report from the Cybersecurity and Infrastructure Security Agency. That’s a scary statistic for any organization, and more so in the public sector, where there’s a high bar setRead… Read more »
How Hackers Are Stepping Up Phishing Attacks (and How to Fight Back)
One of the best defenses against phishing is multifactor authentication (MFA), which requires users to provide something more than a password, such as a biometric scan, a one-time code or an email notification. Sadly, traditional MFA is not as foolproof as people like to think. That conundrum was the focus of a recent GovLoop virtualRead… Read more »
The Open-and-Shut Case for a Cybersecurity Upgrade
Many agencies are bogged down with budget battles, lengthy procurement cycles and outdated technology. That makes it harder to follow federal cybersecurity mandates and protect sensitive data. Download this topic snapshot to discover how your organization can create a prioritized cybersecurity upgrade plan to help your modernization journey. You’ll learn: Effective ways to secure theRead… Read more »
4 Priorities for Effective Identity Management
The term “critical infrastructure” evokes images of power lines and water treatment facilities, but it also applies to the identity management platforms that protect networks from cyber intrusion. At a recent GovLoop virtual event, “Access Denied: How to Improve Your Agency’s Identity Management,” Steve Caimi, Director of US Public Sector Solutions Marketing with Okta —Read… Read more »
Don’t Panic: 5 Doable Ways to Improve Cybersecurity
Just when you think you understand cybersecurity, everything changes. In the case of cyber solutions, that change is always for the better, but it can still feel overwhelming. One simple piece of advice: “Don’t look at it and let that paralyze you,” said Russell Marsh, Director of Cyber Operations in the Office of the ChiefRead… Read more »
Tips and Takeaways: How Automation Can Make Cybersecurity Less Painful
This resource features tips and takeaways about how to combat cyber threats with automation. Download your resource now: Brought to you by:
Why a Human-Centric Approach Is Key to Zero Trust
In an era of remote work and rising cyberattacks on public sector targets, federal, state and local authorities need a new approach to cybersecurity. They’re rethinking their cyber strategies both in order to keep the bad actors at bay, and also to meet the call for zero-trust architectures. In this report, we look at howRead… Read more »
Why Old-School Thinking Can’t Keep Up With New Security Challenges
Check out this new report to learn how agencies’ approaches to security inside systems has changed. You’ll explore how micro-segmentation can better protect your agency.
Your Agency’s Zero Trust Roadmap
The language of cybersecurity can be complicated and full of terminology that a layperson may struggle to understand. But protecting computer systems from cyberthreats — especially government systems — is increasingly critical. This worksheet offers information on what zero trust entails and practical steps you can take to adopt it in language anyone can understand.Read… Read more »
What the Executive Order Means for Cybersecurity
This resource explores five sections about the executive order’s key components aimed at enhancing you and your coworkers’ cybersecurity agencywide. Download your copy: Brought to you by:
Maximizing Your Human and Capital Resource Investments: A Cybersecurity Playbook
Discover four steps toward a collective defense approach for your agency’s cybersecurity. Download your Playbook, Maximizing Your Human and Capital Resource Investments: A Cybersecurity Playbook, now: Brought to you by:
Your Guide to Understanding Gov Zero-Trust Security
How can agencies quickly understand the complexities and nuances of zero-trust security and align with the transformative details in Biden’s EO? We created this playbook to help answer that question.
5 Ways the Cyber EO Will Change How Govies Work
Explore five areas in which the Cyber Executive Order will influence how govies work and how their agencies think about cybersecurity. Download your resource, 5 Ways the Cyber EO Will Change How Govies Work, now: Brought to you by:
Recharging Your Agency’s Cybersecurity With the President’s Executive Order
This quick-tips resource covers the EO’s most critical details and their impact on agencies.
3 Ways to Empower Work From Anywhere
Learn how your agency can secure and support multiple work styles through these best practices.
How to Get Real With DevSecOps
Explore a government case study, best practices and resources to help make DevSecOps a reality at your agency.
What You Can Do Now to Prepare and Persevere Through the Next Cyberattack
Bold – not incremental – changes are needed to address the current government cyberattack landscape. Check out our latest e-book to understand how to ready yourself and your agency for its next cyber incident.
The Policies That Enable Hybrid Teams: cyber Tips & Takeaways
Learn how an agile approach to cybersecurity can empower all employees – wherever they might be working.
Putting Security Front and Center in the New World of Hybrid Work
Preparing for a future that includes more permanent telework means rethinking the way employees connect and collaborate.
Personal Security Amid Cyber Chaos: Tips and Tricks to Stay Safe
Check out this new report to learn the basics for personal cybersecurity.
The 3 P’s of Cybersecurity: Quick Tips to Stay Safe
Explore activities, quizzes and easy tips for vital cybersecurity concepts.
Security for All Things Hybrid: Tips and Tricks to Stay Safe
Get your free copy of this spotlight resource to explore what cybersecurity looks like in the age of hybrid, with personal security tips for home, the office and everywhere in between.
Assessing Your Agency’s Cloud Security
This free worksheet will help you assess your agency’s cloud security.
How to Assemble a Data Protection Strategy Checklist
Learn how your agency can protect its data in this age of sophisticated cyber threats.
The Cyber Aware Workforce
Learn how state and local governments can create a strong line of cyber defense.
Secure, Connected Employees, Resilient Agencies
Reimagine your workspace.
Zero Trust: An Updated Approach to Agency Cybersecurity
Learn how a Zero Trust model can validate connections, track user and device activity and improve your agency’s overall cybersecurity.
Innovations in State and Local Cybersecurity
In this new e-book, you’ll learn what dynamic cybersecurity is and how agencies can use it to stay one step ahead of today’s risks.
Time for Modern, Secure Networks: The TIC 3.0 Initiative
Explore a recap of a GovLoop roundtable discussion featuring TIC 3.0 policy leaders, plus other sources to help you understand the TIC 3.0 policy.
From Ransomware Vulnerability to Resilience
Get your free copy of our new e-book to explore the challenges of ransomware.
GovLoop Explains: What Is Zero Trust?
Zero Trust: what is it? Should your agency be implementing it? Watch this short explainer to find out.
Worksheet: Best Practices for Getting Started With DevOps
Download your copy of this free checklist for seven tips that will provide practical guidance and useful hints to jumpstart the transition at your agency.
Understanding Your Threat Intelligence Maturity Level
Cyberattacks are on the rise and protecting against these attacks is a priority of every government agency at all levels. Knowing your threat maturity level can help you understand your organization’s strengths and weaknesses as you work towards fully integrated threat intelligence. This new worksheet will help you discern where your organization lies on theRead… Read more »
Worksheet: Grading Your Agency’s Cloud Readiness
GovLoop created this tool to measure your agency’s cloud readiness, using the federal government’s Cloud Smart strategy for inspiration.
Worksheet: Filling the Skills Gap to Develop a Cyber Workforce
GovLoop created this resource to help your agency understand which skills gaps it must address to fill its shortage of cybersecurity professionals.
Cyber Awareness Checklist
Share this checklist with employees at your agency. If they cannot mark each of these tactics off their list, give them the appropriate contact information for your IT or cybersecurity help desk so they can be better prepared to tackle cybersecurity in their daily responsibilities.
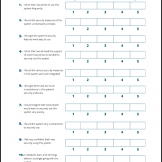
Cybersecurity Usability Assessment
This template is a modified version of the System Usability Scale. Use it as a quick way to assess the cybersecurity and usability of your technologies and services for non-IT professionals.